DWroidDump: Executable Code Extraction from Android Applications for Malware Analysis - Dongwoo Kim, Jin Kwak, Jaecheol Ryou, 2015

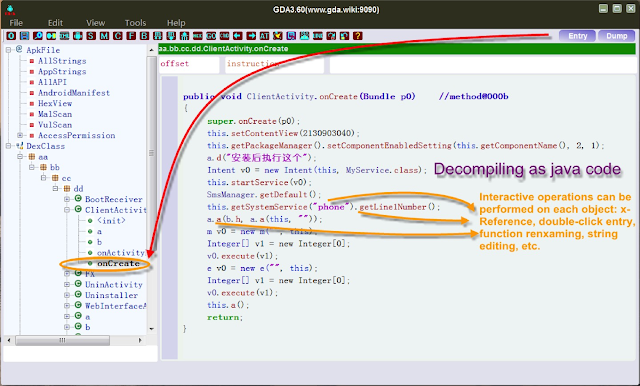
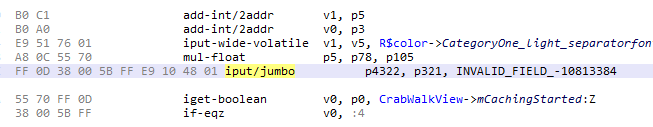
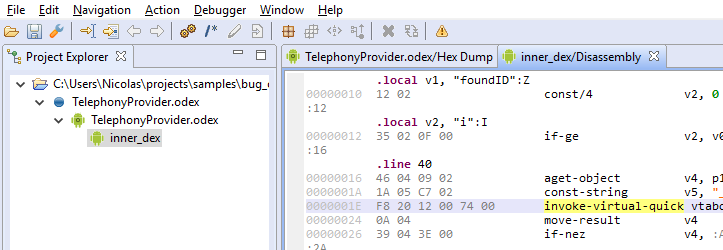
DWroidDump: Executable Code Extraction from Android Applications for Malware Analysis - Dongwoo Kim, Jin Kwak, Jaecheol Ryou, 2015
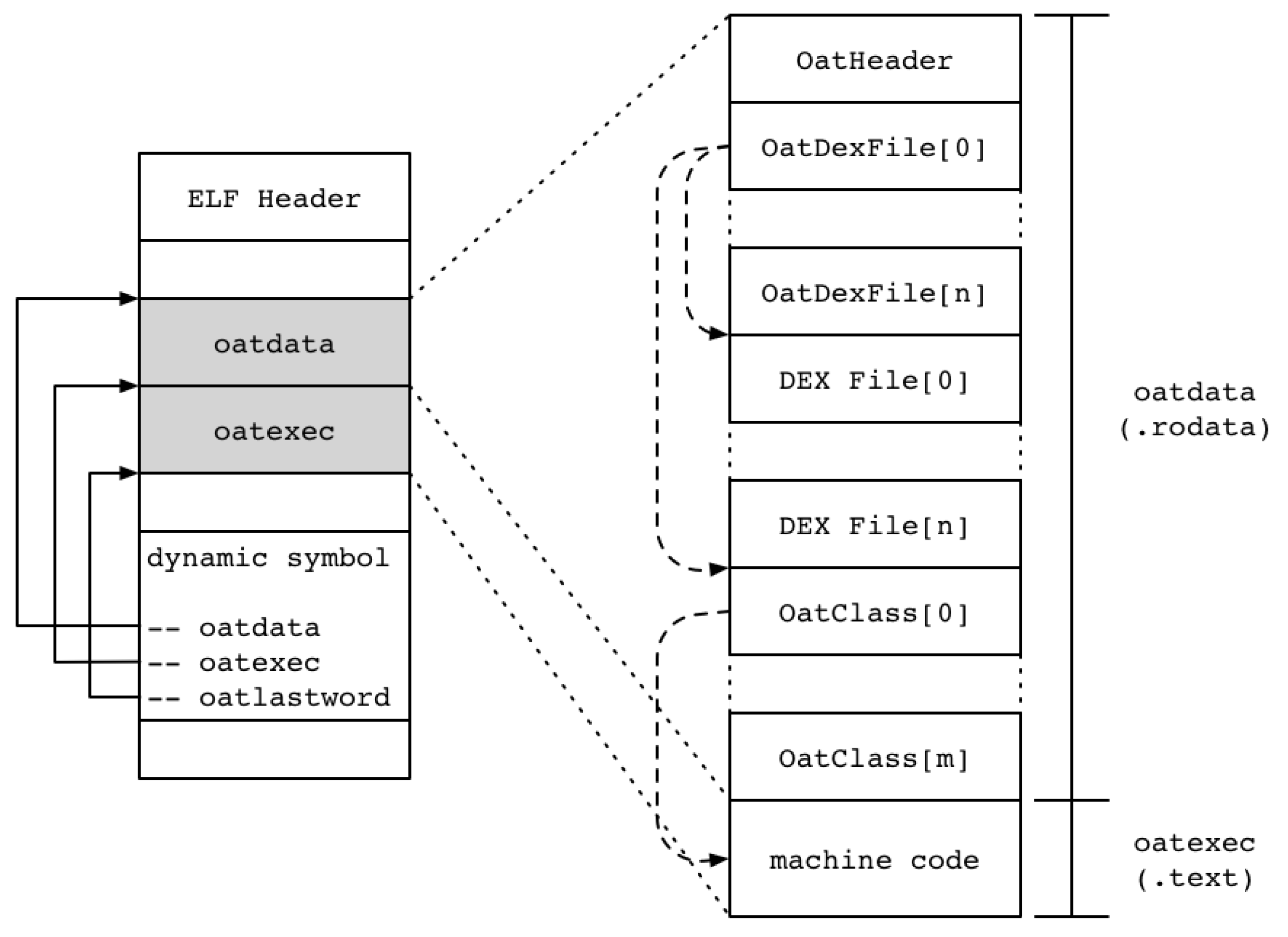
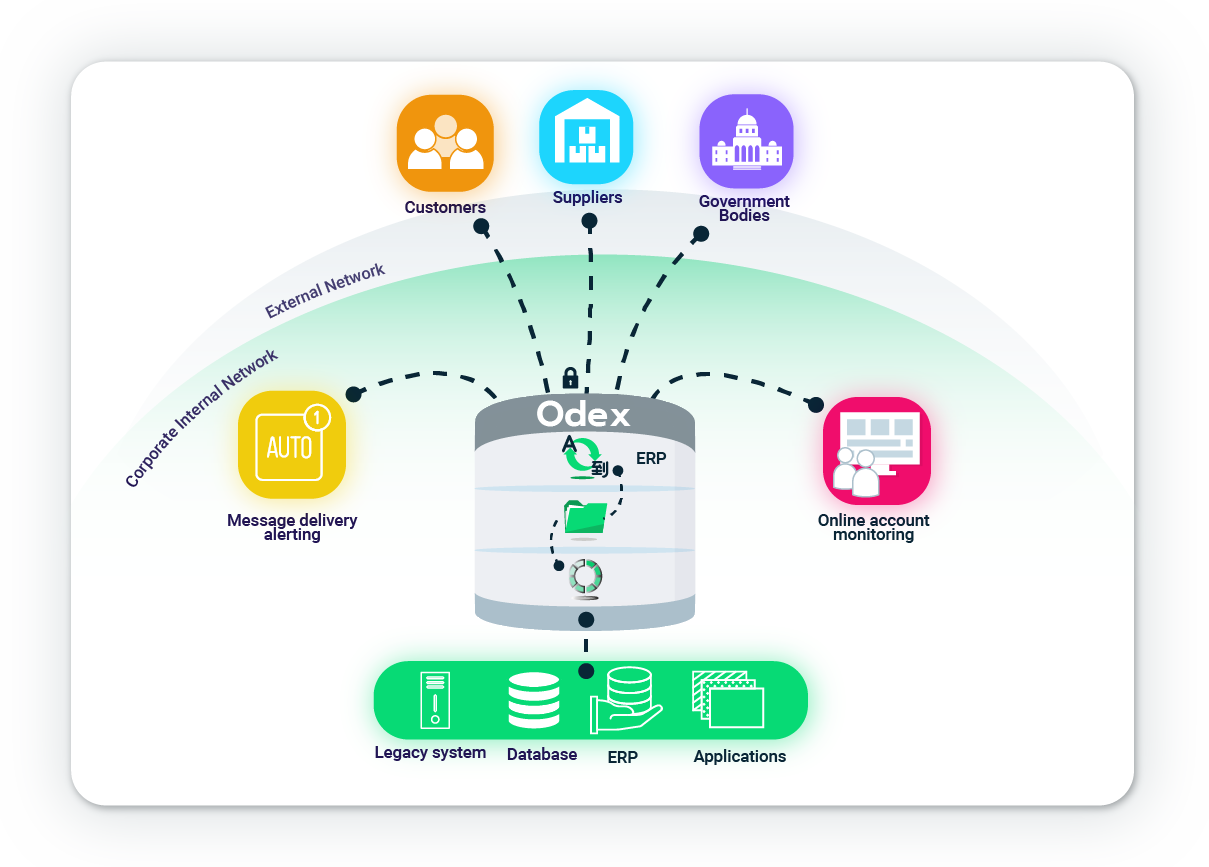
What is a .dex file? What is dexopt? What is odex? What is dexoat? What is ELF? How does this all work? - Quora